About the Project
Eliminating Security Bottlenecks through Reachability Intelligence.
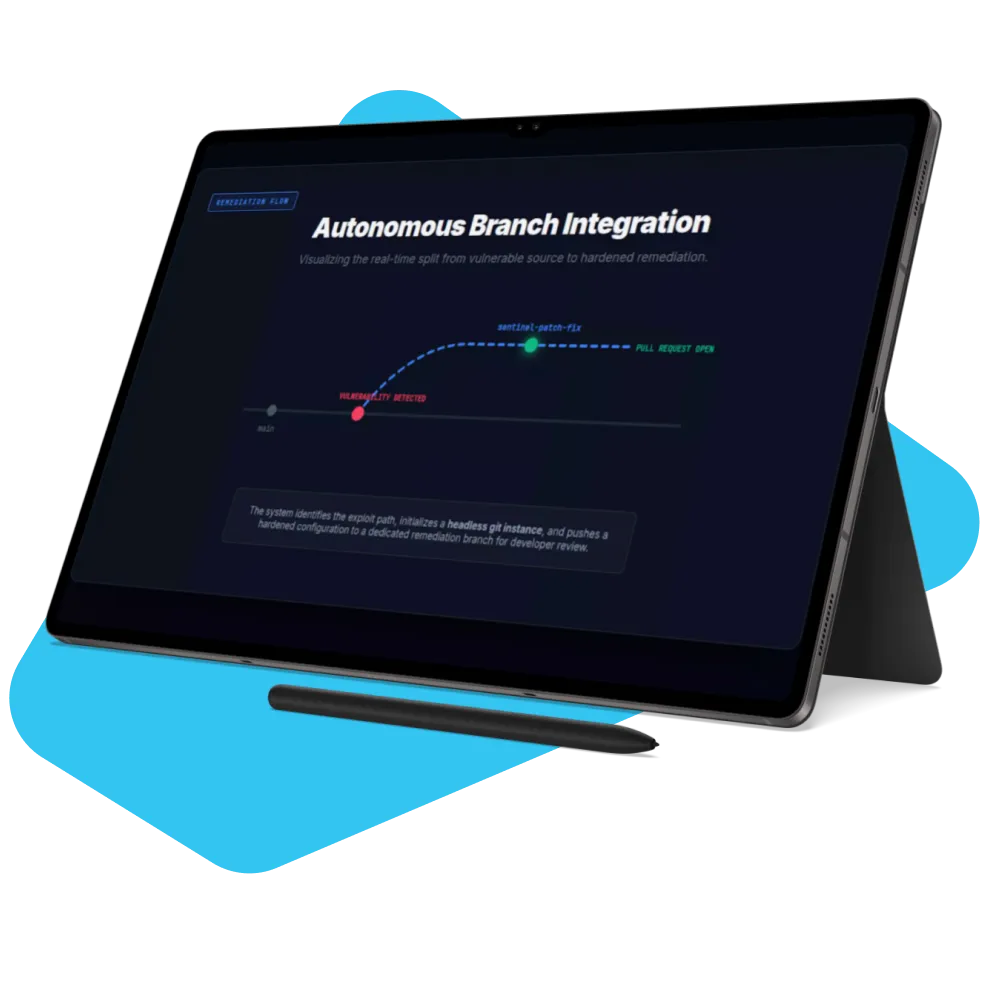
The project aimed to solve the “Broken Window Paradox” in DevSecOps: where critical threats are missed because security teams are overwhelmed by thousands of non-exploitable alerts. By focusing on Execution Path Analysis, we addressed the gap left by traditional scanners that only check for files on a disk. The result is a self-healing pipeline that not only detects threats but autonomously opens remediation Pull Requests to harden the environment. For teams comparing DevSecOps vs DevOps, this project shows why security automation should be treated as part of engineering delivery, not as a separate approval layer.
Project Challenges
Building this autonomous environment required solving several unique challenges in the vulnerability management lifecycle:


Severe Alert Fatigue : The client's legacy Node.js environment was flagging over 1,800 vulnerabilities per scan. Manually triaging this volume was impossible for their security team, leading to critical supply chain risks being ignored.



Supply Chain Poisoning : Traditional manual updates were too slow. An attacker could exploit a known vulnerability in an outdated base image (Node:14) before the team even finished triaging the weekly scan report.



High False-Positive Rates : 99% of the flagged vulnerabilities existed in system libraries (like Perl or OpenLDAP) that the application never actually executed. We needed a way to distinguish between "vulnerable on disk" and "exploitable in memory."



Remediation Resistance : Developers were hesitant to patch images because they feared breaking dependencies. We needed a system that validated the fix by comparing "Before" and "After" states to prove the security value without breaking the app.
How Did We Help?
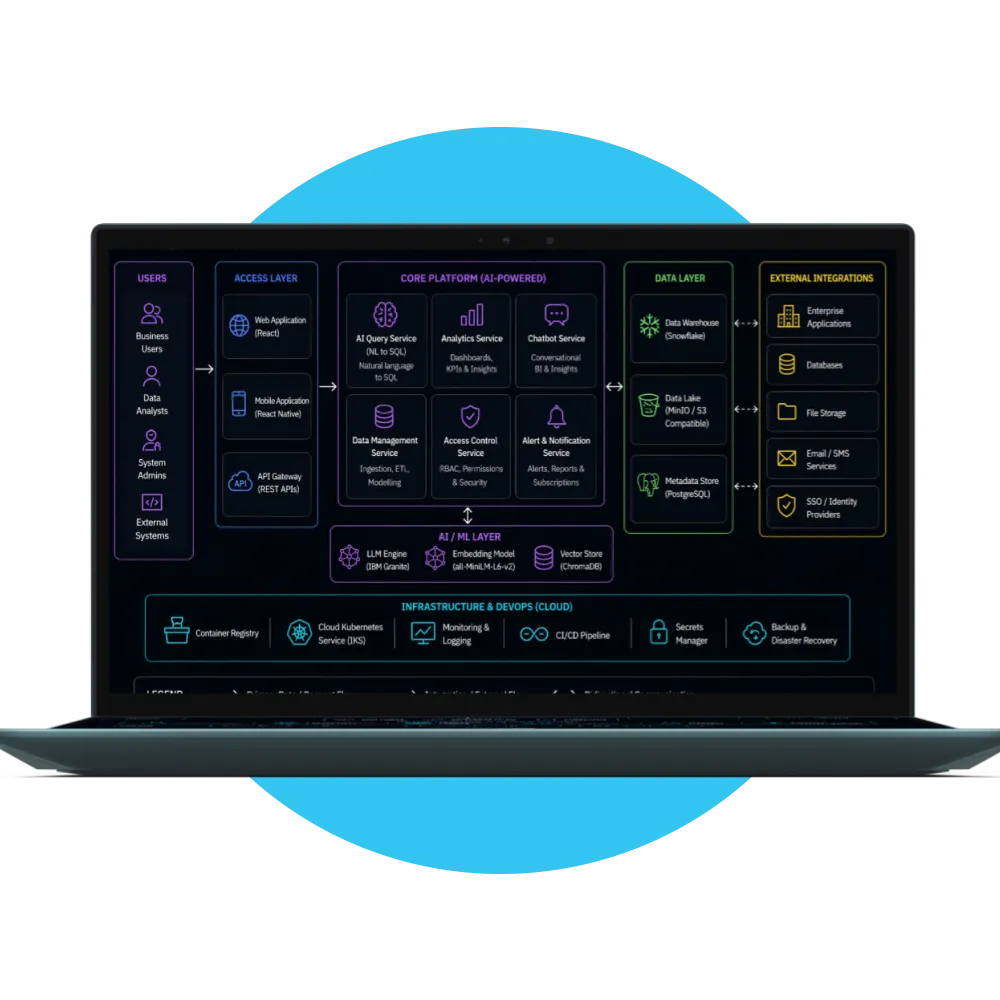
We approached the development with a phased DevSecOps strategy to reduce vulnerability noise, automate remediation, and create a compliance-ready security workflow.
The outcome
The project emerged as a model for modern DevSecOps, replacing a “scan-only” culture with a “remediation-first” ecosystem. This shift is also an important step in the DevOps maturity model, where teams move from manual, reactive operations to automated, measurable, and continuously improving delivery systems.
- Noise Reduction: Reduced alert volume from 1,811 theoretical risks to 4 reachable threats (99.7% reduction).
- Deployment Speed: Reduced the Mean Time to Remediation (MTTR) from 5 days to under 30 seconds.
- Compliance Ready: Automated the generation of HTML audit trails, making the project ready for SOC2/ISO27001 audits.
- Zero Downtime Patching: The autonomous PR workflow ensures that security hardening happens in parallel with development, never blocking the release cycle.










Ethan Walker
“The Sentinel-Patch engine transformed our security posture overnight. We went from being buried under 2,000 alerts to having a self-healing pipeline that identifies and fixes reachable threats before we even start our morning meetings. It is the most intuitive approach to vulnerability management we’ve ever seen.”